Shodan - 14 Years Later, It's Still a Hackers Best Friend

Shodan is a search engine for internet-connected devices. Officially launched in 2009 by John Matherly - Shodan has easily remained one of my favorite tools for discovery and OSINT throughout my offensive security career. When executing the discovery phase of a pentest - Shodan can be incredibly useful for finding assets that have been forgotten, neglected, or are unknown to the organization. Shodan works by scanning and collecting information about anything connected to the internet. You query Shodan like you would any other search engine. Shodan has syntax, similar to google, that will help with quickly locating whatever it is you're searching for. If you're not looking for anything specific - no problem, you can find enough to keep you entertained for hours on end. The Shodan bots (crawlers) work 24/7, so when you query Shodan you are getting the latest picture of the internet. Cool, right? The crawlers are located all over the world - so this helps to prevent geographical bias. If I've garnered your attention, let's quickly step into Shodan features and search syntax.
Please note - even though the items found on Shodan are public - I've refrained from adding screenshots to this article that show excess information. Additionally - use general precaution and common sense. While the items shown on Shodan are publicly viewable, the assets themselves are not and explicit permission would be required. IANAL, follow all local ordinances, state and federal laws, etc. The information within this post is for educational purposes only.
Before we dive in - be aware that some of Shodan's functionality is restricted to Shodan members. Membership generally costs around 50 US dollars (one-time fee) and can often be obtained during annual sales (Black Friday). Basic search functionally is restricted to users with an account, so at the very minimum you should create a free account.
What can Shodan be used for?
Network Security: keep an eye on all devices at your company that are facing the Internet
Market Research: find out which products people are using in the real-world
Cyber Risk: include the online exposure of your vendors as a risk metric
Internet of Things: track the growing usage of smart devices
Tracking Ransomware: measure how many devices have been impacted by ransomware
Source: What is Shodan? - Shodan Help Center
I'd add entertainment to that list. With a quick search you can find some pretty wild results.

Shodan Search Basics
With a simple search on Shodan, you're provided the results of Shodan's crawlers. Shodan does NOT include meta-data unless you specifically tell it to. You can narrow down results by including search filters, bringing in some of the meta-data as needed. Filter syntax is simple: filter:value
Listed below is a small set of common search filters you should check out.
city: find devices in a particular city, like Detroit.
city:"San Diego"
country: find devices in a particular country. Looking for devices in the US?
country:"US"
http.html:"Wordpress" - Websites that have the word "Wordpress" in their HTML
geo: pass Shodan coordinates
has_ssl: boolean based search for ssl
has_screenshot:true: boolean - show devices that have screenshots.
hostname:"hostname here" - Find values that match a specific hostname
net: search based on an IP or /x CIDR
os: search based on operating system
os:"Windows 7" os:"windows server 2012" os:"linux 3.x os:"Synology"
port:8000 - Find particular ports that are open.
port:80,443
product:"MySQL" - MySql Servers
before/after: find results within a timeframe
org:"Org Name Here" - Search for assets owned by an organization.
Combining filters
To enhance your search query, you can combine various filters. To find assets within the United States that have an http title of "login" with port 443 or 80 open you could use the following query:http.title:Login port:443,80 country:"US"
Want to narrow it down to only sites running Wordpress? Simple: http.title:Login port:443,80 country:"US" http.component:wordpress
Am I Exposed?
Want to see what ports are open on your IP address at home? Use this link: http://me.shodan.io
A 404 Not Found response indicates you're not exposed.
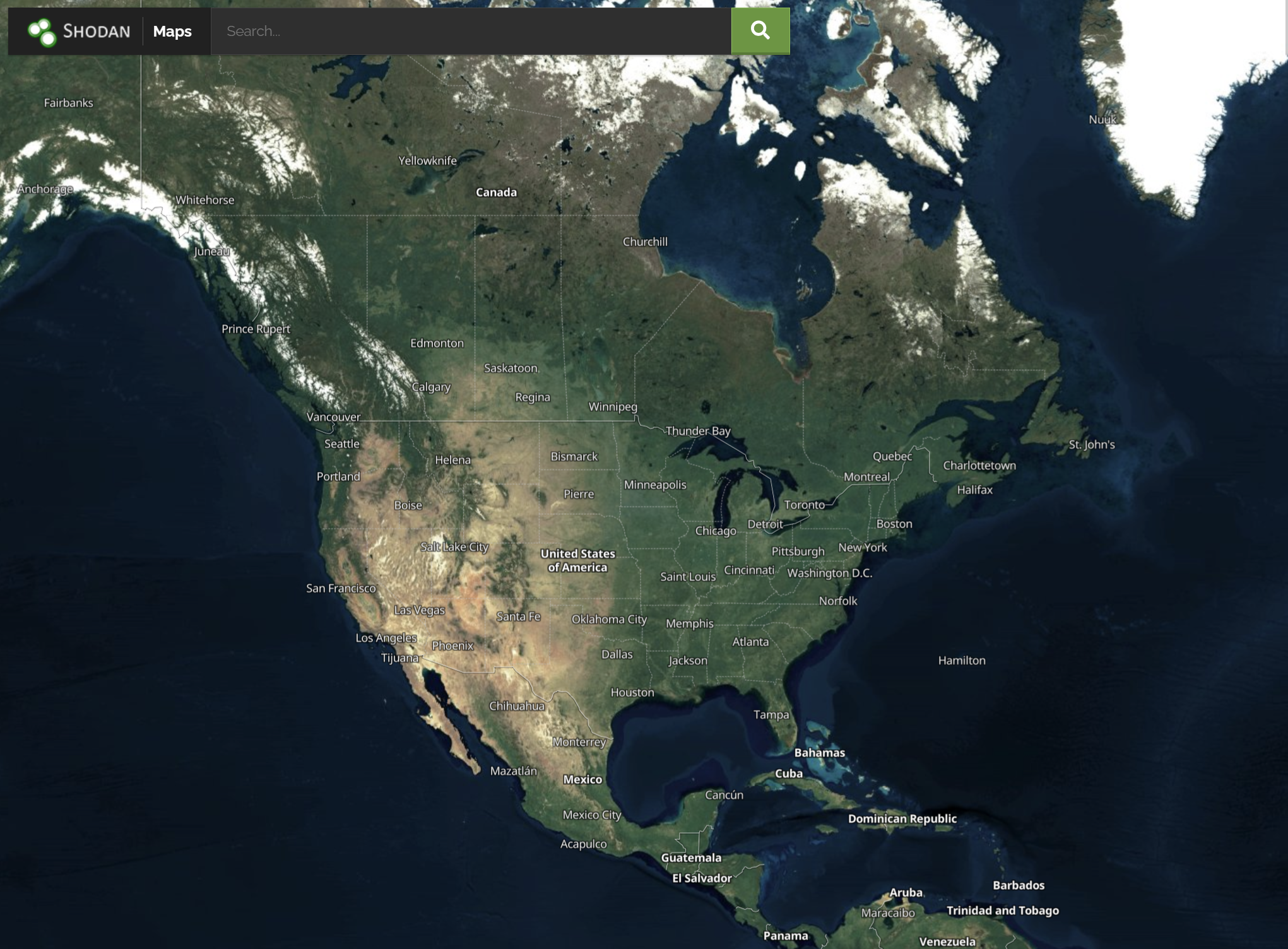
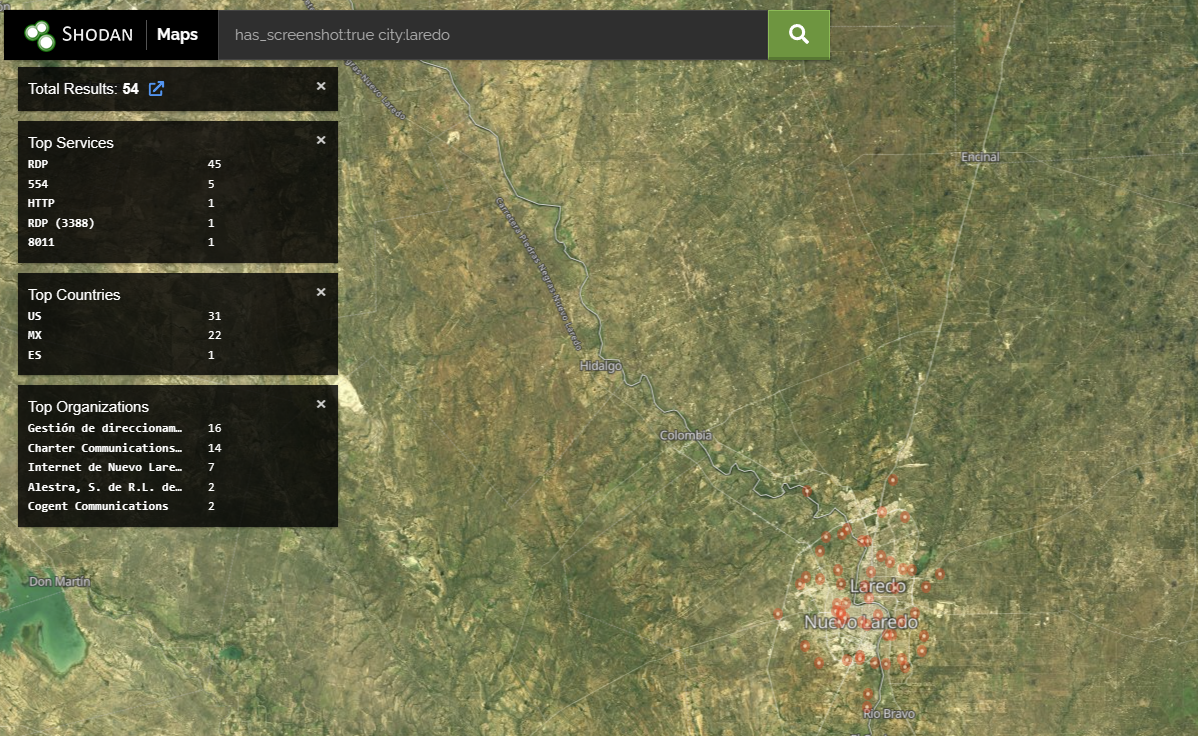
Shodan Maps
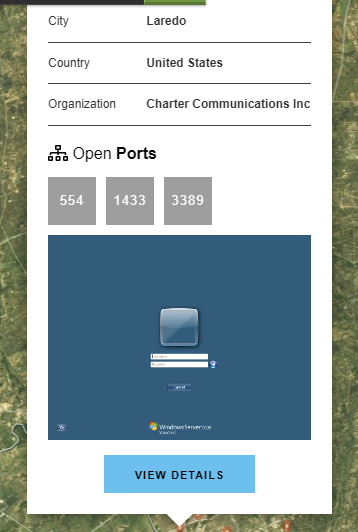
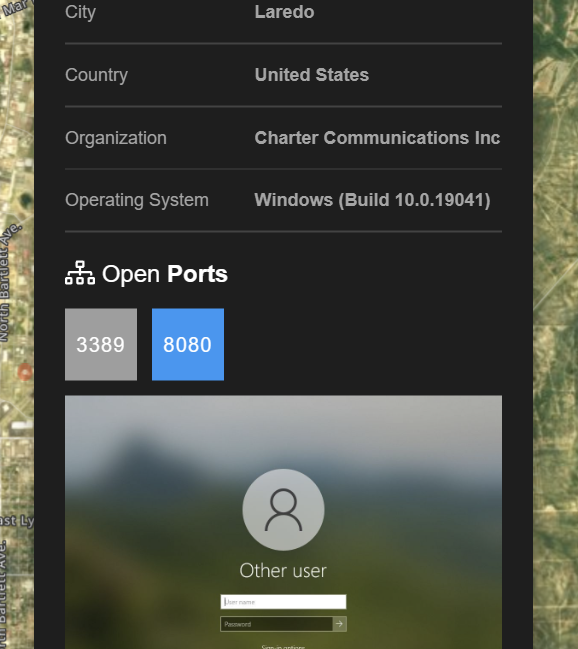
Want to search by location? Use Shodan maps. Pair this with the has_screenshot:true filter and take a look around. Shodan grabs meta-data about the devices it index's, such as: location, hostname, operating system, etc. The maps subdomain allows users to search based off the location data captured.
Screenshots
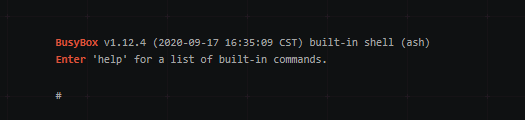
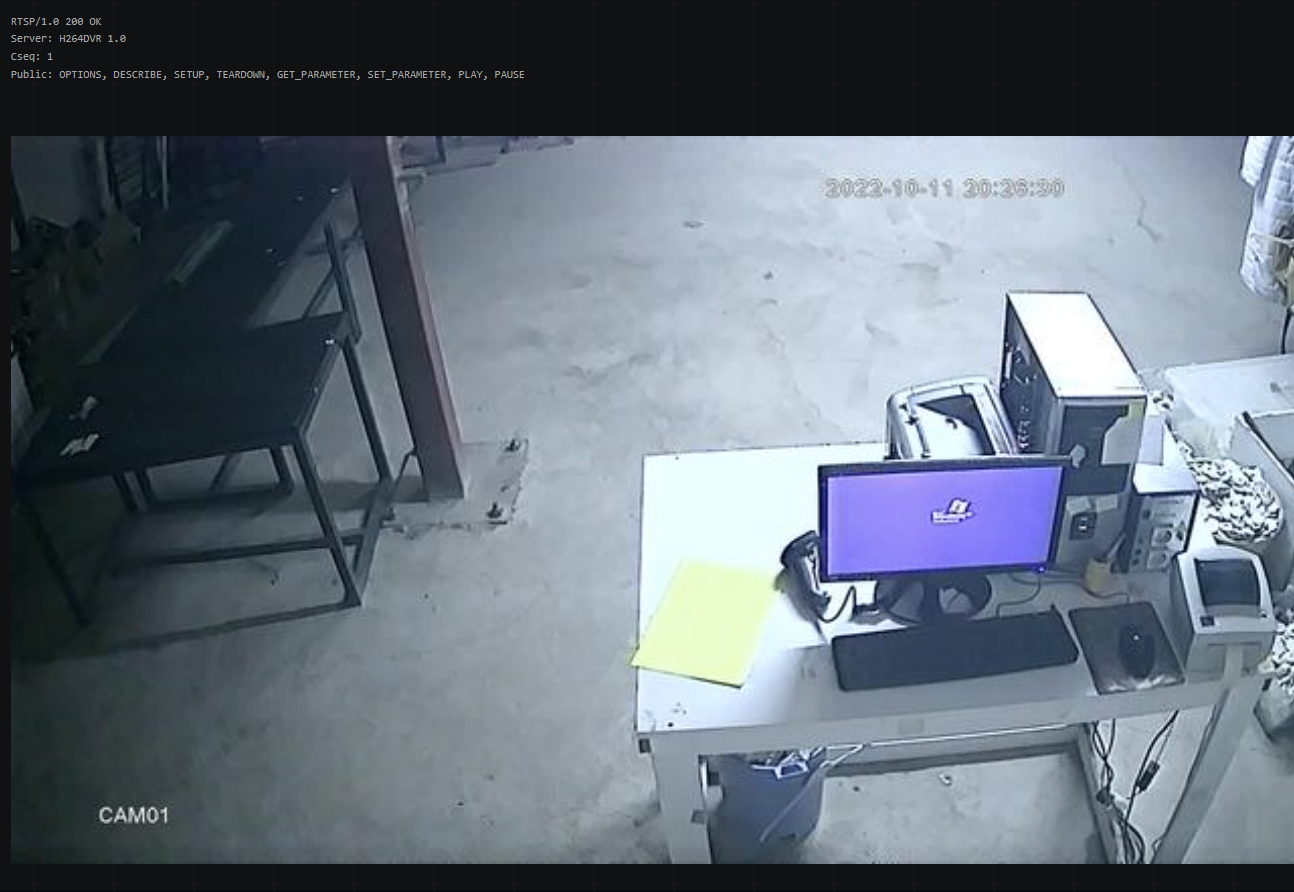
Shodan collects screenshots from various sources (RDP, VNC, etc.) For a quick glance, use the images portal.
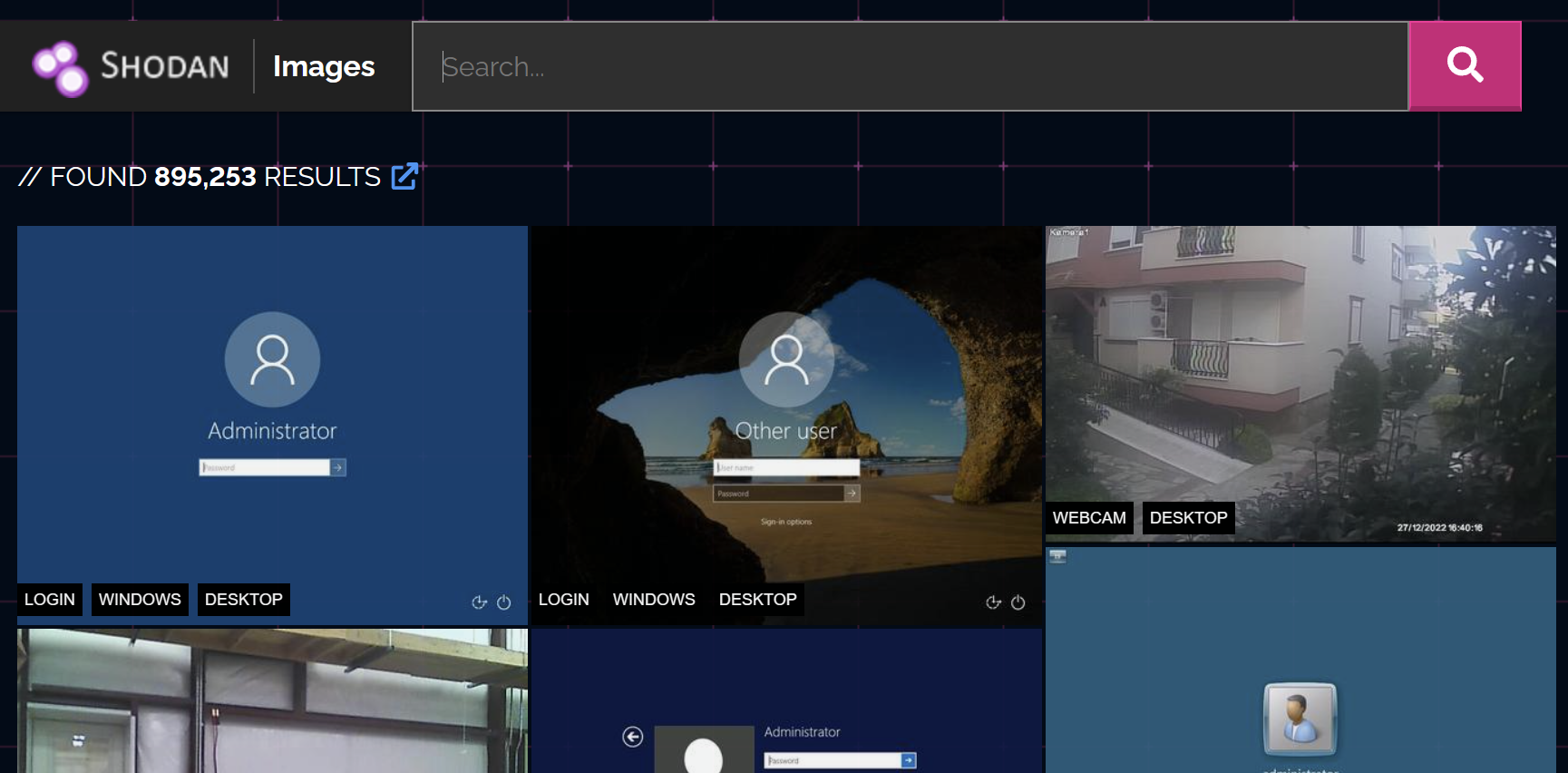
Screenshot labels
When using has_screenshot:true, combine it with screenshot labels for additional filtering. For example, you could search for items within Mexico that contains a screenshot and is labeled as "desktop":
has_screenshot:true country:"MX" screenshot.label:desktop
Or maybe you want to find items within Mexico that have screenshots but are not labeled as a desktop: has_screenshot:true country:"MX" -screenshot.label:desktop



Listed below are screenshot labels I find useful.
screenshot.label:desktop
screenshot.label:login
screenshot.label:windows
screenshot.label:terminal
screenshot.label:webcam
screenshot.label:loggedin
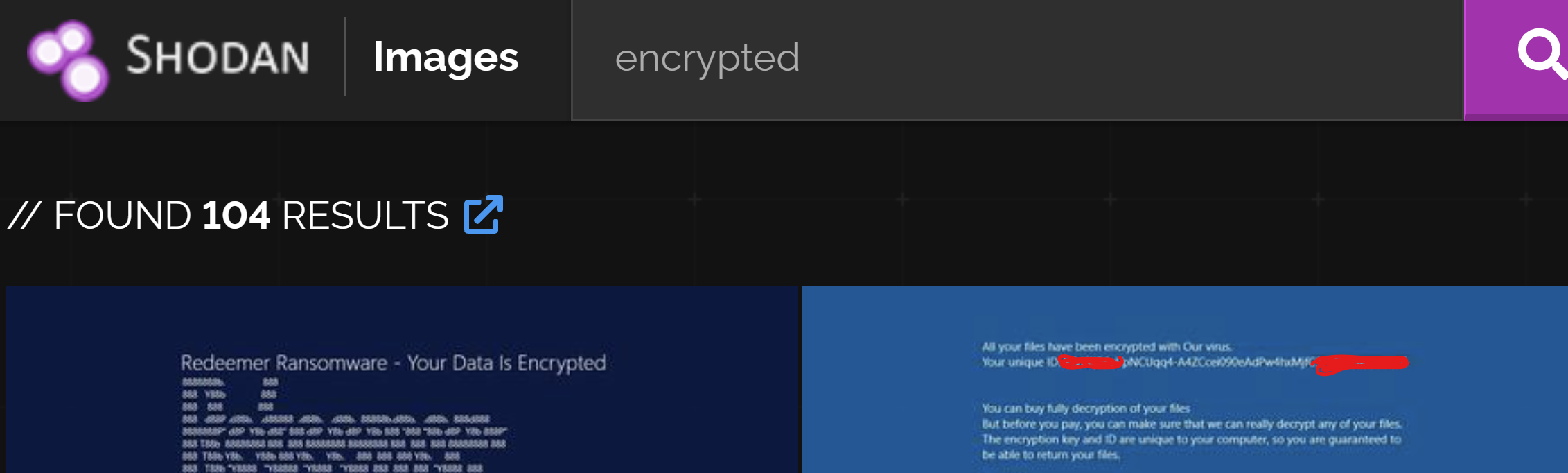
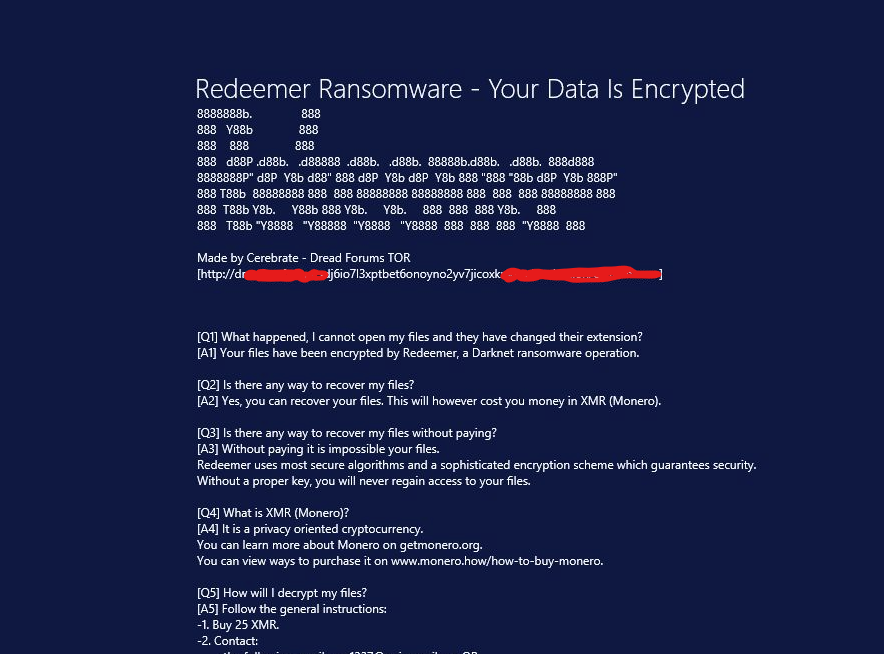
has_screenshot:true -screenshot.label:desktop -screenshot.label:webcamOptical Character Recognition
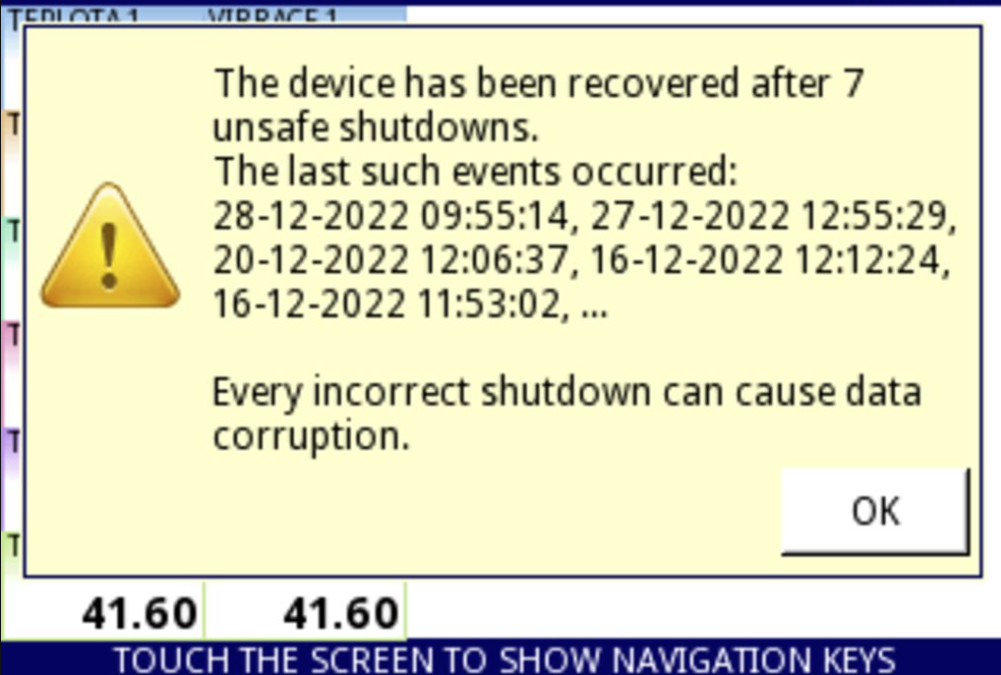
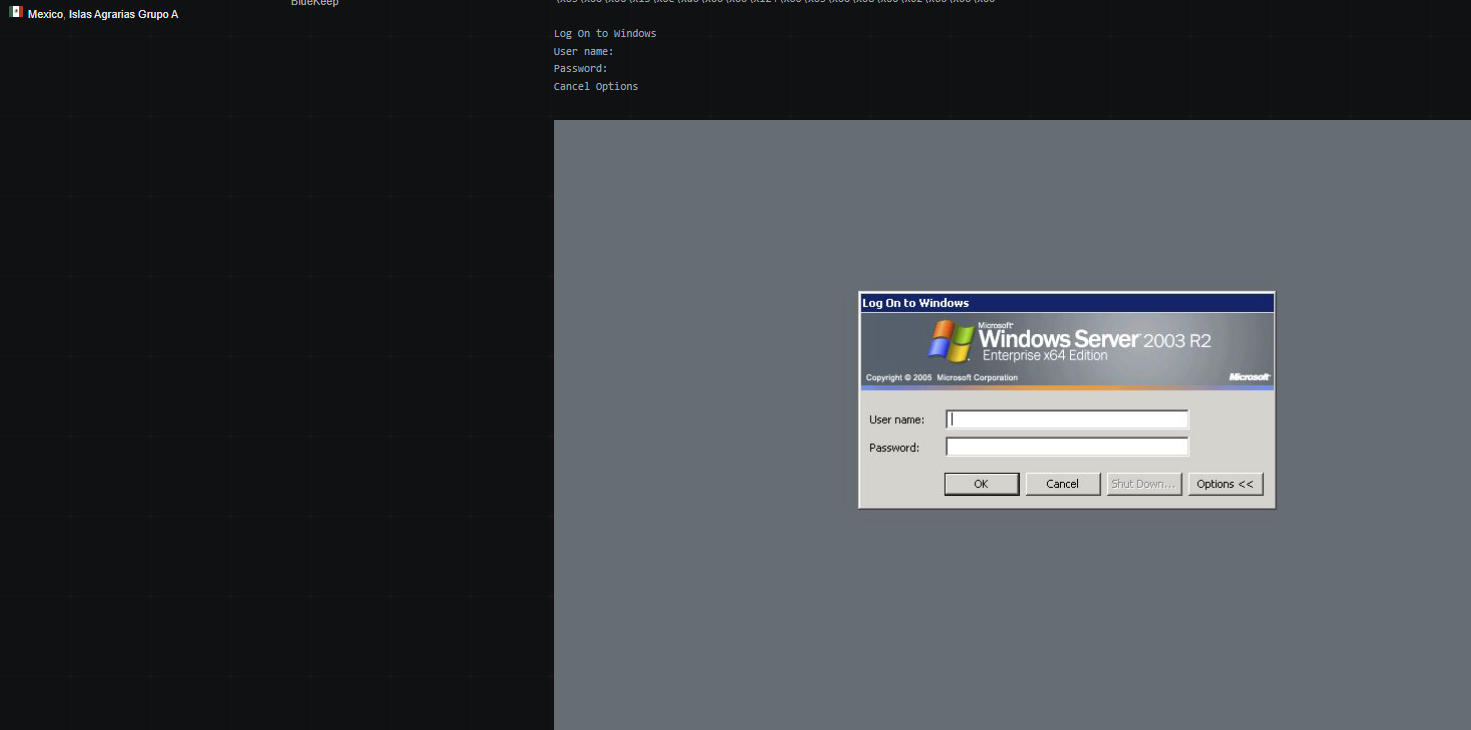
Shodan performs OCR on images, and then stores that data in the banner. This allows users to search for text within images. One use case for this is finding hosts infected with ransomware:
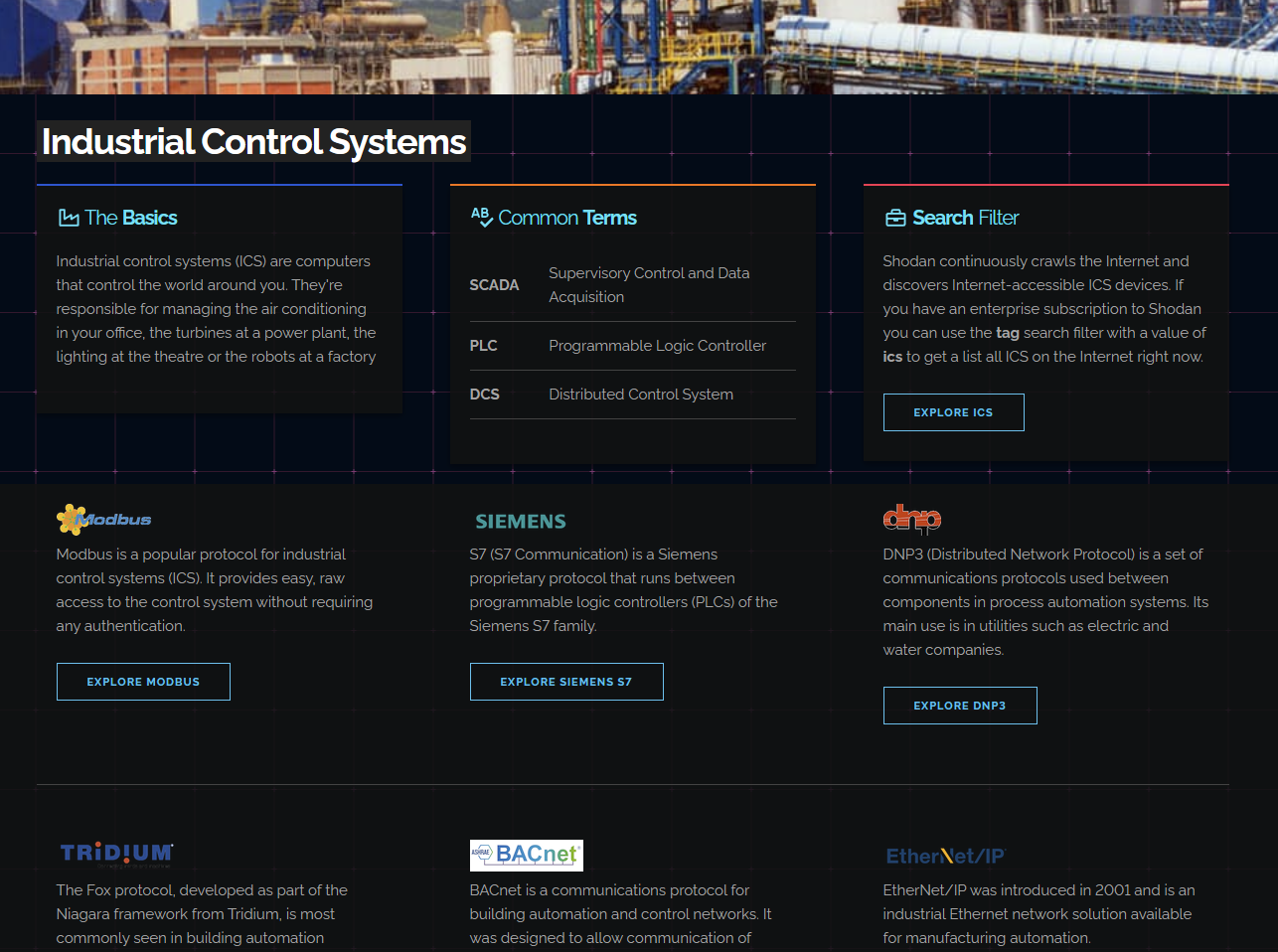
Looking for ICS?
screenshot.label:pos
screenshot.label:ics
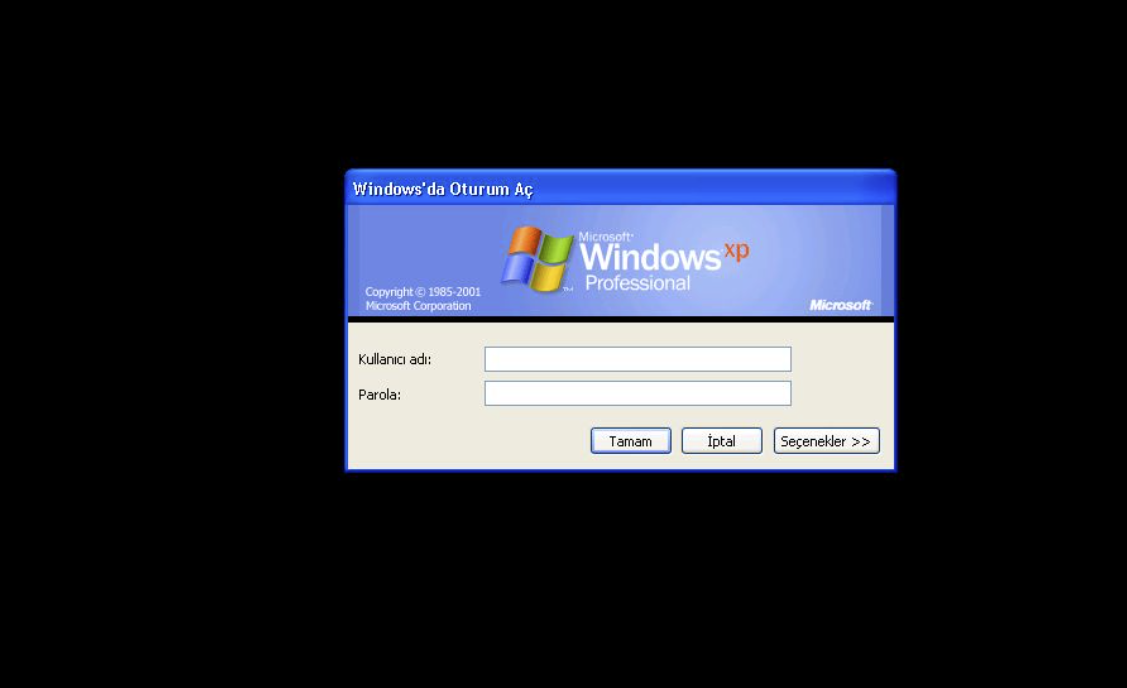
Windows XP, Server 2012 (etc)?
os:"Windows 5.1" - Windows XP, example here
os:"Windows 2012" - Windows Server 2012, example here
Reference this Wikipedia article for versioning details.
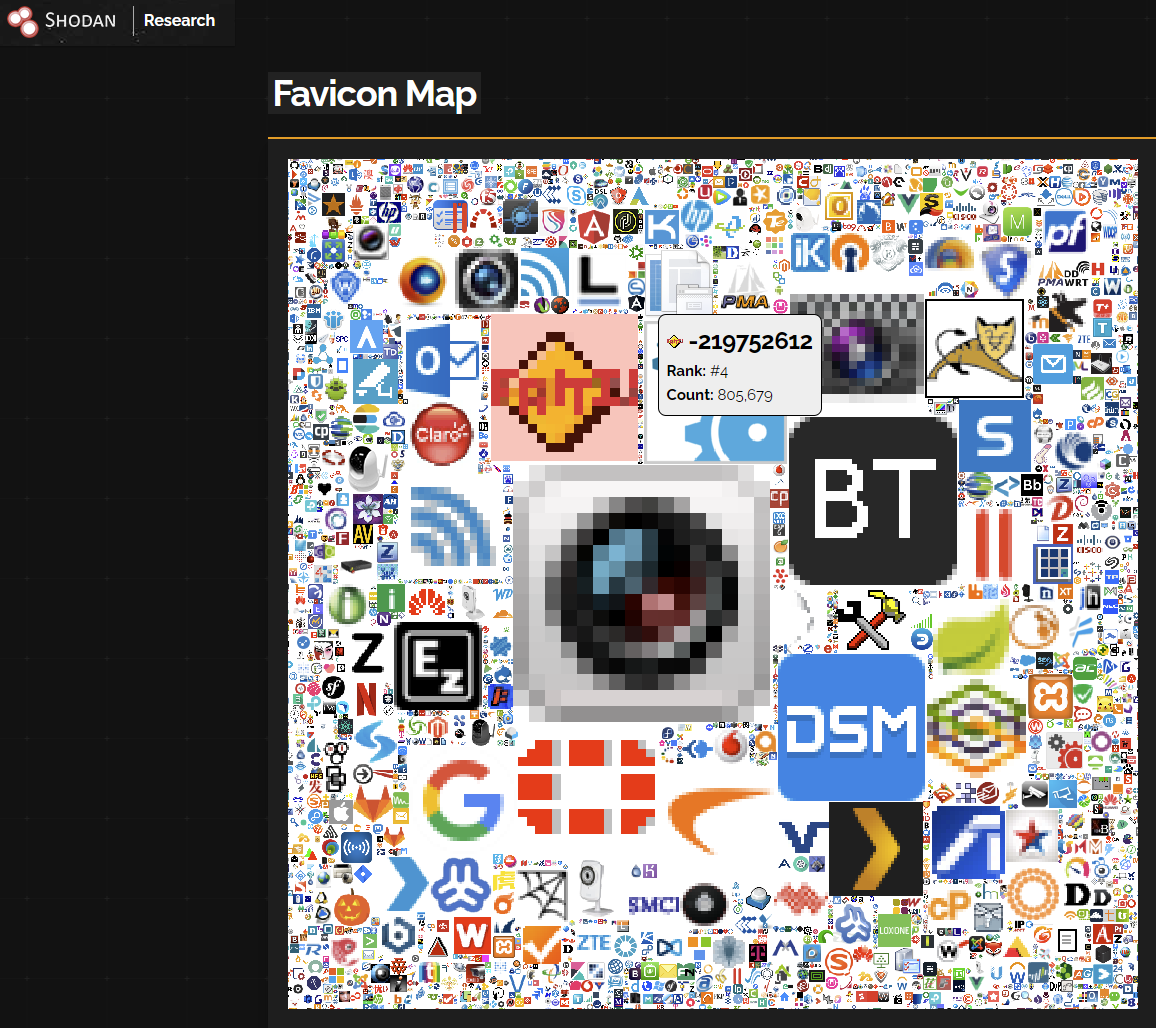
Favicon Maps?
Yep - Shodan collects favicons and maps them to a hash value for easy searchability. Below is an example of a search to find plex instances:
http.favicon.hash:-895890586
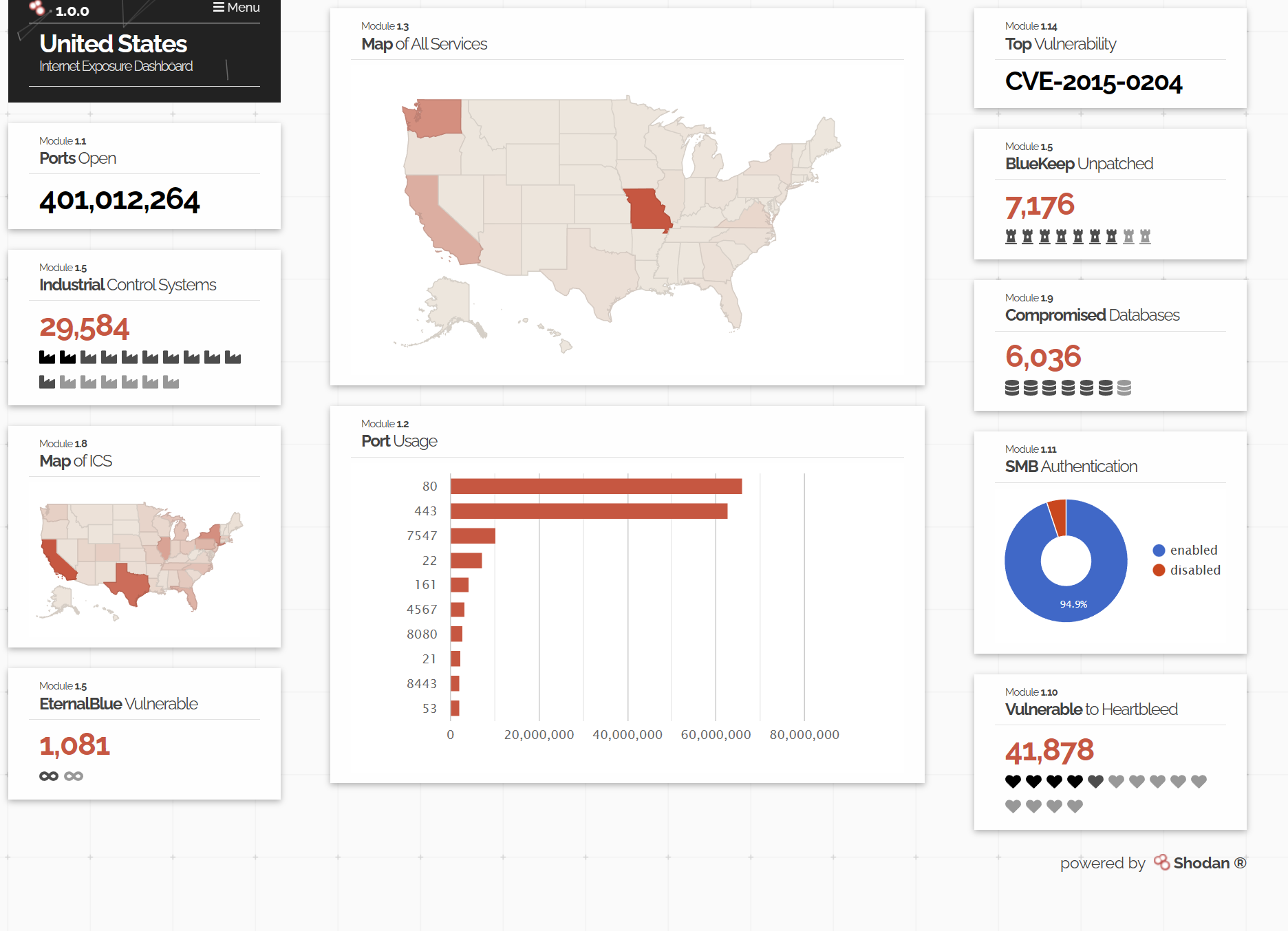
Exposure Models
Yes - check them out here. The internet exposure observatory lets you see what services a country is exposing.
External Resources
Listed below are some of the best online resources I've found for Shodan related dorks.
The Complete Guide to Shodan
If you would like to dive deeper into Shodan's features, search syntax, and available services you can take a look at the official Shodan book - found here. Please note that this reference was last updated in 2017.
Filter Reference: https://beta.shodan.io/search/filters
Search examples: https://beta.shodan.io/search/examples
If you host a website and want to learn more about what data Shodan crawlers collect? Check out the Shodan datapedia.

